Google has confirmed that it's testing a password-free way to sign into a Google account. The approach allows users to authenticate by responding to a notification sent to their smartphones.
It's no secret that passwords are the weak link when it comes to account security, with poor hygiene, credentials theft and hacker tools for brute-forcing accounts all conspiring to make them ineffectual enough to need back-up with another authentication form.
In fact, a recent CompTIA survey showed that employees tend to practice poor password protection, with the research showing that 38% of workers have repurposed work passwords for personal purposes. Further, 36% of employees use their work email address for personal accounts. This generates more points of exposure for organizations, and can be difficult to address without better training to spur behavioral changes.
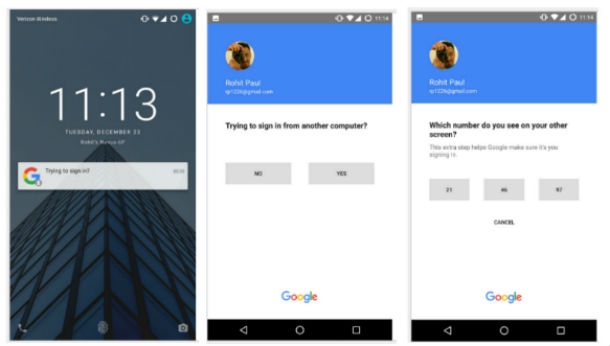
Google's idea is to allow users to enter only their email address when signing in; they will subsequently receive a mobile notification asking if they approve the log-in. They will be signed in once they tap "yes."
The trial was first reported by a Reddit user Rohit Paul. He said that he was sent an email invitation to join a test group called "Sign-In Experiments at Google" and given access to try the new technology on his own device.
A Google spokesperson confirmed the testing to TechCrunch.
We've invited a small group of users to help test a new way to sign-in to their Google accounts, no password required. "Pizza", "password" and "123456"—your days are numbered.
—the spokesperson said.
Users can continue to use typed passwords if they choose (and testers can leave the trial at any time); and, Google said that it could choose to ask for a password as an additional security measure at any time.
Yahoo is testing something similar, dubbed "Account Key" which uses a notification sent to the user's phone to open an app, which in turn allows the user to approve the log-in.






